Israel-based cybersecurity company Paragon Solutions and its alleged surveillance software “Graphite” have recently come back into the spotlight following an image shared on social media. According to claims circulating online, a selfie posted by company employees on LinkedIn inadvertently revealed what appeared to be a Graphite control panel in the background. The image spread quickly, reigniting debate over the capabilities of commercial spyware tools.
So what is Paragon Solutions, how is Graphite described, and what could this alleged dashboard leak signify?
What kind of company is Paragon Solutions?
Paragon Solutions Ltd. is known as an Israel-based cyber intelligence and surveillance technology company. The company reportedly provides its products to government agencies and security services rather than to individual customers. In public-facing materials, Paragon emphasizes its focus on combating terrorism and organized crime.
In this respect, Paragon is often compared to firms such as NSO Group, which previously drew global attention with its Pegasus spyware. These companies develop advanced mobile surveillance tools and license them to state institutions.
What is Graphite and what is it alleged to do?
Graphite is described as Paragon’s commercial surveillance product. Reports by cybersecurity research groups, including Citizen Lab, and various international media outlets have suggested that Graphite can extract data from targeted mobile devices.
According to these claims, Graphite can:
- Access message content on targeted phones
- View communications from end-to-end encrypted apps such as WhatsApp, Signal, and Telegram
- Collect contact lists, call logs, and other communication data
A key distinction emphasized by experts is that such tools do not necessarily “break” end-to-end encryption directly. Instead, they may gain access to data at the device level — either before encryption is applied or after messages are decrypted and displayed on the screen. In other words, the target is typically the device itself, not the encrypted transmission channel.
What does the LinkedIn dashboard image allegedly show?
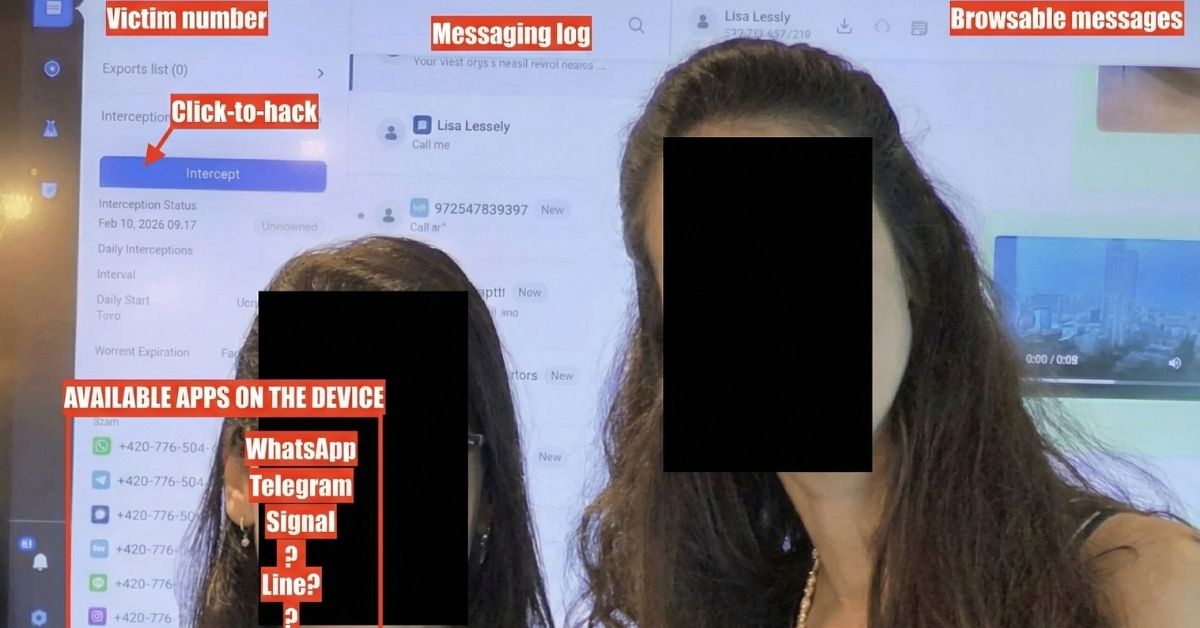
According to social media claims, a selfie taken inside Paragon’s office inadvertently captured a computer screen displaying what was alleged to be a Graphite control panel.
Screenshots shared online reportedly show:
- A field for selecting a target phone number or user
- A panel listing message content
- Buttons suggesting one-click access or activation of monitoring
However, there has been no independent technical verification confirming that the interface indeed belongs to Graphite. Therefore, caution is warranted when assessing the authenticity and scope of the image.
The Meta and WhatsApp connection
Meta previously disclosed that it had detected targeted attacks against certain WhatsApp users and suggested a possible link to Paragon’s Graphite spyware. Around 90 individuals were reportedly targeted, including journalists and civil society figures.
This development revived concerns that commercial spyware tools might be used not only against criminal suspects but also against journalists, activists, and other members of civil society.
Is end-to-end encryption really being bypassed?
Applications such as WhatsApp, Signal, and Telegram rely on end-to-end encryption, meaning that only the sender and recipient can read the messages.
However, according to cybersecurity experts, advanced surveillance tools may avoid directly breaking encryption algorithms. Instead, they may exploit operating system vulnerabilities to:
- Capture keystrokes before messages are sent
- Intercept notification content
- Extract local message databases
- Take screenshots of decrypted conversations
In this scenario, encryption itself remains intact, but the device becomes compromised.
What does this mean for digital security?
If the alleged LinkedIn dashboard image is authentic, it suggests two important points:
- Commercial surveillance tools may feature highly user-friendly interfaces.
- Even companies specializing in cyber operations can face operational security risks due to human error.
It is also important to note that such spyware is generally used for targeted surveillance operations. Conducting indiscriminate mass surveillance would involve significantly different technical and financial considerations.
Ongoing debate, limited verification
Paragon Solutions and its Graphite software represent another chapter in the global debate over commercial spyware. The alleged LinkedIn dashboard leak has raised new questions about technological capabilities, ethics, and legal boundaries.
However, without independent forensic verification, the circulating images cannot be treated as conclusive evidence. Further analysis by cybersecurity researchers and official statements will be essential to clarify the situation.
In the digital age, the fundamental question remains unchanged: How can societies balance security needs with the protection of privacy?